Cyber Security vs. Data Security: The Key Differences

Data security and cybersecurity are not the same things. But, there is a lot of overlap between data security details and cybersecurity details. One of the main facts about the distinction is that data security deals with securing digital information perimeters against attacks from getting in or out.
In contrast, cybersecurity protects against breaches caused by scenarios related to the Internet. “Data,” in this case, can be anything on any media; it may even be printed on paper if it’s still stored in electronic format (like an image file) but copied onto the material for easy viewing/printing purposes.

This is why they’re referred to as ‘data’ and not ‘physical files.’ A more precise definition would be: “Data is any kind of information that has been stored on a computer-readable medium or transmitted through electronic media.”
- Data Security: In deciphering data security meaning, it refers to a practice or process that protects data in storage, in transit, and during processing; it is the process of keeping unauthorized people from accessing your information.
- Cyber Security: Cybersecurity focuses more on safeguarding electronic networks such that attacks by hackers can be avoided. It also involves protecting government systems, especially when linked with other government sites over an open network.
Both of them are necessary for businesses because they are two sides of the same coin. They are both useful in their ways. Data security is used to protect data by ensuring it remains within certain boundaries. Cybersecurity deals with keeping intruders out to prevent their access to an entire network or a device connected to a network.
In cybersecurity, encryption is one of the security mechanisms used in transforming data using an algorithm to make it difficult for unauthorized individuals/entities/systems to read/interpret. The transformation occurs when you change numbers into a secret code or make the data appear gibberish (like random letters and symbols).
In data security, the primary focus is data protection regarding how it is handled and stored. It also deals with securing your information from physical threats like theft or damage to storage devices, as well as making sure that illegitimate users cannot break into systems and read/alter data. Data security has five main aspects: secure modes of operation, permission lists, access codes/passwords, encryption, and auditing.
Again in cybersecurity, encryption ensures that the information stored is not accessible by unauthorized persons. It transforms data so that no unauthorized person can understand the information you stored on them.
Summary of the Difference between Cyber Security and Information Security
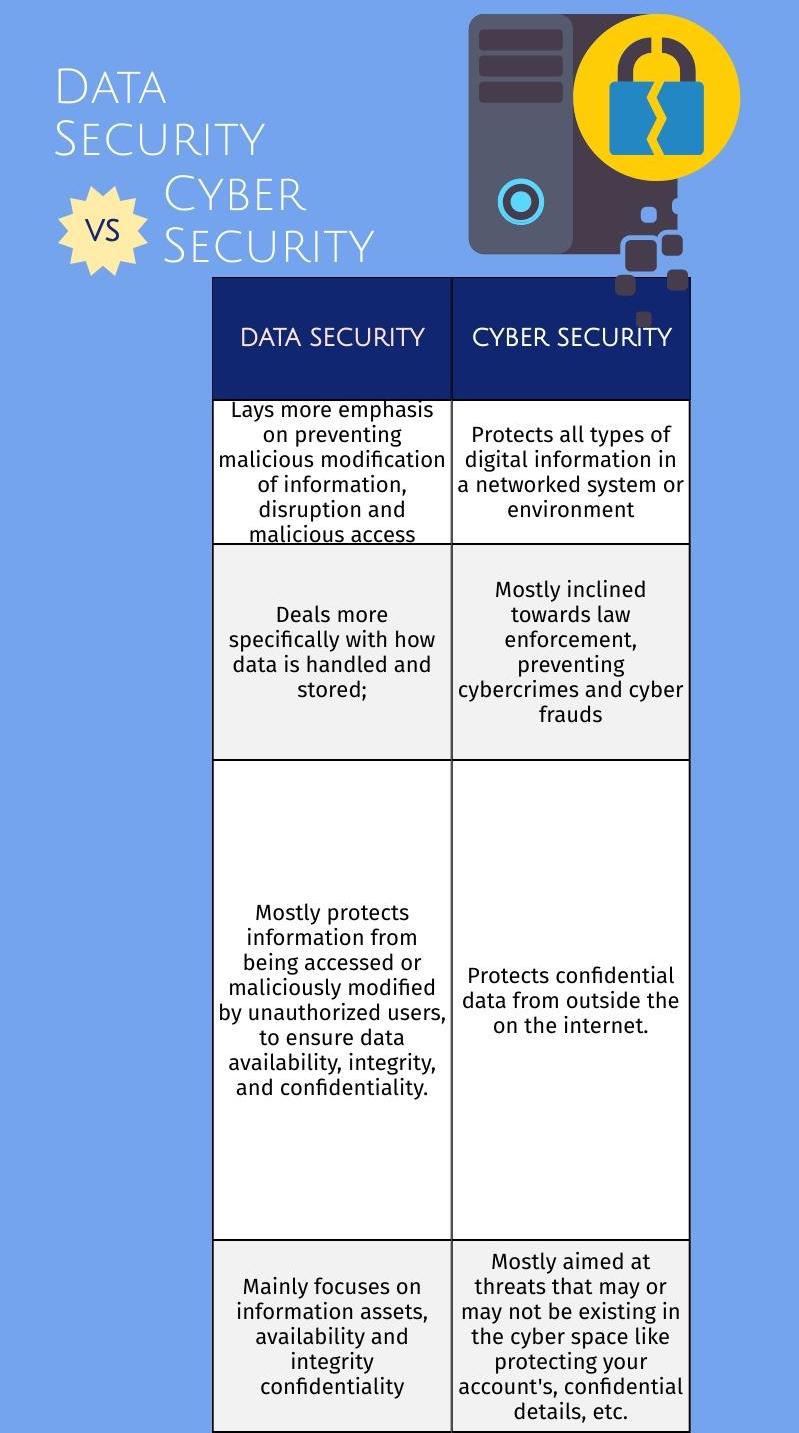
- Cybersecurity deals with the protection of all types of digital information in a networked system or environment.
- Cybersecurity is mainly inclined towards law enforcement, preventing cybercrimes and cyber frauds.
- Data security emphasizes preventing malicious modification of information, disruption, and malicious access, among others.
- Data security deals more specifically with how data is handled and stored; it also ensures that no illegitimate users can break into systems to access/manipulate data.
- Cybersecurity experts use encryption algorithms to transform original text or numbers into codes that only authorized people can unlock – this way, sensitive data is safe from being accessed by unauthorized individuals. This doesn’t happen on its own, however. You have to have anti-virus software installed so your computer won’t be invaded by malware.
- Encryption is not always used in data security but is one of the common ways to keep your data protected. For example, if you want to store important documents on a flash drive or an external hard drive so you can take them anywhere with you and work on them offline – make sure that these storage devices are adequately encrypted.
How does SSL Work with Cyber Security and Data Security?
The Secure Socket Layer protocol, also known as SSL or TLS, is the standard security protocol used to encrypt data sent over a communication channel between two machines. The protocol also allows client authentication and digital signatures and is used on more than 90 percent of websites in 2021.
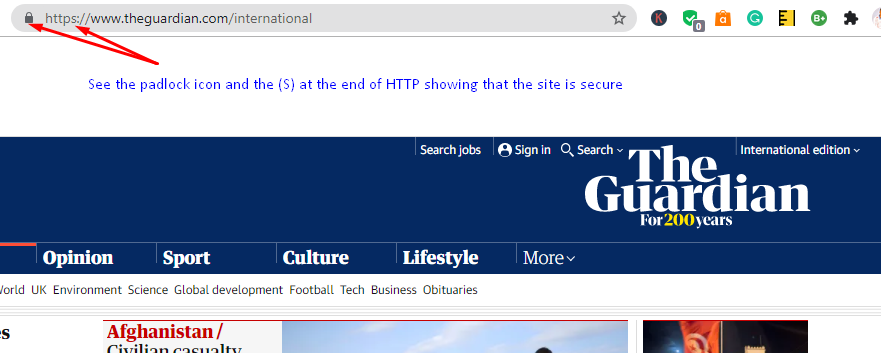
SSL enables HTTPS – HTTP Secure – or Hypertext Transfer Protocol Secure that protects the privacy and ensures that the content received from websites is not intercepted, modified, or forged by any third party, including hackers (e.g., viruses) between your computer and theirs or even eavesdroppers on public Wi-Fi networks in cafes, airports, etc. Using recent versions of browsers such as Google Chrome, Firefox, Internet Explorer and Microsoft Edge, you can see the browser bar icon on websites that are secured with SSL.
If you are a business owner who processes sensitive information or accepts payments on your website, you need to purchase an SSL certificate to use the SSL technology. You can also check if a website uses a secure server by simply looking at the URL, which starts with “https” instead of “HTTP. “Some other ways to confirm this is that,
1) The https: or // prefix is shown in the web browser’s location bar
2) The website address (URL) line shows https:// and not HTTP:// before the domain name – for example, https://alibabacloud.com/ instead of http://alibabacloud.com/
3) There is a padlock icon on the web browser.
Security Benefits of SSL Certificates in Data Security and Cyber Security
The features of SSL certificates in cybersecurity vs. data security are best understood when considering their benefits to businesses. For example, SSL provides:
- Encryption & data integrity: Protection of sensitive information as it is transmitted between a customer and the website
- Client authentication: The ability to verify that a website is authentic and not fraudulent
- Digital signatures: The ability to track transactions, warranty, and return privileges
- Improved trust: Your website won’t show any warning signs, which will make it more trusted by users
- Search engine ranking improves after adding SSL certificate: Popular search engines incline towards user security, implying that you may get preferential treatment if your website guarantees safety for web users.
- Increased conversions: SSL certificates can help you reduce bounce rates on your website, which will help increase your overall conversion rates.
How do Certificates Work?
Trust is everything in online shopping or any other kind of electronic transaction. This is where SSL certificates from reputed certificate authorities (CAs) like Comodo SSL certificate, Thawte SSL, GeoTrust Certificates, RapidSSL Certificates come into play.
They offer an encrypted tunnel of protection against cyber-attacks such as identity theft, eavesdropping, etc., ensuring that your data and identity are safe. If you are a website owner running an ecommerce site, SSL Certificates issued by trusted Certificate Authorities afford you increased sales volumes as customers have more confidence in doing business with you.
Similarly, if your business operates on the Internet and conducts sensitive transactions from online forms or offers a confidential service such as consultation for legal advice, doctors, etc., or if you accept credit card payments online, then it is time to get an SSL certificate that will ensure protection for all these services.
This is particularly necessary considering the increasing risks of cyber-attacks on businesses. Here’s a summary of how best SSL certificates can improve your data security or cybersecurity landscape:
- A person trying to eavesdrop on communications between two computer users will only see useless encrypted text, not the actual data being passed back and forth. This ensures that communication remains private and cannot be cracked by hackers.
- A fraudster setting up to impersonate an ecommerce website and then steal payment information or credit card details by capturing sensitive data will not be able to do so because the SSL Certificate can only be used by the true owner of the service which a trusted third party has verified. Once this verification is complete, online shoppers know they are on a secure site. Preventing impersonation can help you prevent massive losses through phishing attacks, one of the most favored attack mechanisms by cybercriminals. More than 85 percent of businesses are targeted in phishing attack schemes.
- The server itself could have been compromised with a virus that might infect the users’ computer as soon as one enters sensitive information such as passwords, credit card numbers, etc., but that won’t happen if you use SSL technology. This ensures customers feel confident about doing business with you because their personal details always remain protected during transactions performed on your site.
- Data integrity ensures that no alteration, distortion, or falsification of data is possible as it is sent and received between the user’s computer and the company’s server; hence businesses can rely on their customers to have correct information about products or services offered without needing to worry about a third party manipulating it in some way.
- The convenience of using SSL technology makes doing business online so much easier than ever before because verification takes place from beginning to end without interruptions which mean transactions are quick and easy with lower risks for potential fraud threats, thus making the customer experience more pleasant.
The Bottom Line
Both cybersecurity and data security are necessary for the smooth running of any online business. As a rule, therefore, none of them should replace the other. As a conscious business owner, it would help if you take the necessary steps to keep your audience’s confidential data online safe.